How to Recover Deleted Files on Android — Restore Photos, Videos & Documents
Stop using the handset at once: enable airplane mode, unmount and remove any microSD card, avoid taking pictures or installing apps. Each write operation on flash storage dramatically reduces the odds of getting items back – a freshly removed microSD has >90% chance of successful recovery when imaged immediately; internal user storage on non-rooted devices commonly yields 10–40% success, while rooted access can raise that to 60–90% depending on overwrite.
Check cloud sync first: inspect Google Drive, OneDrive, Dropbox and any OEM cloud account for synced images, short clips and office/text files – many gallery apps and backup services keep deleted entries in a trash folder for up to 30–60 days. If you loved this short article and you would certainly such as to get additional info relating to 1xbet promo code free bet kindly visit our website. If nothing appears, prefer a sector-level copy before any scanning: for removable cards use a USB adapter and create an image on a PC with dd or ddrescue (read-only), then run recovery against the image.
Recommended tools and sequence: for microSD use PhotoRec/TestDisk (free) or R-Studio on the image; for internal user storage consider DiskDigger on rooted handsets, or use ADB to pull /data/media after enabling USB debugging on devices where that’s possible. Paid desktop suites (e.g., EaseUS MobiSaver, Dr.Fone) may help when immediate imaging isn’t feasible, but always work on a copy. Use low-level imaging flags (for example: dd if=/dev/sdX of=card.img bs=4M conv=sync,noerror status=progress) and keep the original read-only.
Avoid rooting or flashing unless you understand the risks: rooting can improve scan depth but may overwrite recoverable content and void support; if you lack confidence, image the storage and hand the image to a data-recovery specialist who accepts raw disk images.
Immediate actions to maximize recovery chances
Power off the device or switch to Airplane Mode at once to stop any background writes to internal storage; if the battery must remain connected for imaging, keep the device offline and avoid opening apps.
If a removable microSD card is present: power down, remove the card, mount it in a USB card reader and create a bit-for-bit image on a PC using a read-only mount. Example: dd if=/dev/sdb of=card.img bs=4M conv=sync,noerror (work on the image, not the original card).
For internal (non-removable) storage, do not install or run data-recovery utilities on the handset. If USB debugging is already enabled and you can trust the host machine, produce an image directly to the PC to avoid extra writes: adb exec-out su -c “dd if=/dev/block/mmcblk0 bs=4096” > device.img.
Check registered cloud services and app-specific trash bins immediately via their web interfaces: Google Drive Trash (retained ~30 days), Google media bin (images and clips retained ~60 days), OneDrive Recycle Bin (~30 days), iCloud Recently Deleted (~30 days), and any messaging app backups. Do not rely on the device app alone.
If the device uses adoptable/internal encryption for an SD card, do not attempt to read the card on a PC–the content is tied to the device keys and must be imaged from the original handset or processed by specialists who can image encrypted partitions.
Keep the battery charged above ~20% if you expect to image the device yourself or hand it to a lab; avoid system updates, automatic app updates and new app installations that create additional writes.
If sending the handset to a recovery service, provide the unlock PIN/password or keep the device unlocked for imaging and request a documented chain of custody; if you prefer not to disclose credentials, inform the service so they can advise on chip-off or other hardware methods (these are more invasive and costly).
Always create and work from a verified forensic image or a copy of the original media; use write-blockers where available and verify image integrity with hashes (md5/sha256) before attempting any analysis or restoration on the copy.
Power off or enable airplane mode
Power off the smartphone immediately; if powering down is impossible, switch to airplane mode and manually turn off Wi‑Fi and Bluetooth before touching any apps or storage.
Powering off halts system processes that write to internal flash (media scanner, app caches, automatic backups, update services) and prevents network sync or remote wipe attempts from overwriting erased content. Flash storage uses wear‑leveling and background garbage collection; every additional write increases the chance that previously removed blocks get overwritten.
If you must use airplane mode, follow these steps: enable airplane mode, then open quick settings and disable Wi‑Fi and Bluetooth toggles (many systems let those radios be reenabled while still in airplane mode). Next, disable account sync in settings and close all running apps from the recent/app switcher. Do not open the camera, messaging, email, cloud or social apps.
If the handset has a removable SD card, eject it immediately and store it in an anti‑static bag; use a USB card reader and image the card on a separate computer with sector‑level tools. For non‑removable storage, avoid installing or running any recovery utilities on the phone – connecting via USB can trigger MTP and create writes. Instead, power off and consult a desktop-based extraction workflow or a professional service.
If the device is managed (company MDM) or linked to remote‑wipe services, remain offline and powered off until you have a plan for extraction; do not charge, update, or sign back into accounts, and do not hand the device to others without explaining the need to preserve its current state.
Oppo A15s Android Version — What Android Does It Run? | Specs & Updates
Key hardware and connectivity: MediaTek Helio P35 (MT6765) processor; display ~6.52 inches HD+; memory options 3 GB or 4 GB RAM; internal storage 32 GB or 64 GB with microSD expansion up to 256 GB; battery capacity approximately 4230 mAh; rear camera array typically 13 MP + 2 MP + 2 MP; front camera ~8 MP; side-mounted fingerprint reader and dual-SIM 4G support.
How to confirm current software state: open Settings → About phone → Software information to view the vendor skin name and the base mobile OS release number (listed as the platform release). Record the build number and security patch date before proceeding.
Safe installation steps: 1) sync accounts and copy photos/videos to a PC or cloud; 2) connect to reliable Wi‑Fi and charge above 50%; 3) use Settings → Software update for OTA; if OTA is unavailable, download the full ZIP from the official support page and flash via the official recovery image; 4) if moving between major platform releases, perform a factory reset after flashing to avoid stability problems.
Expect vendor support for this entry-level model to include roughly one major platform upgrade and periodic security patches for about two years from launch; if on an older build beyond that window, consider official service-center flashing, verified third-party security patches, or community firmware only if you accept warranty and stability trade-offs.
Oppo A15s Android Version – What Android Does It Run? Specs & Updates
Use the stock ColorOS 7.2 (based on Google’s mobile OS 10) and keep security patches current; switch to third‑party builds only if you can unlock the bootloader, accept warranty voiding, and are comfortable with manual flashing procedures.
Verify installed firmware by opening Settings → About phone → Build information; record the ColorOS build string and the security patch date. Create a full backup of photos, contacts and app data before any change.
Safe upgrade checklist: back up to cloud and local storage; charge battery to at least 60%; connect to stable Wi‑Fi; free a minimum of 4 GB internal storage for the package; disable battery saver. Use Settings → System upgrade → Local install for official packages or the vendor’s PC recovery tool for sideloading. Always confirm the package checksum before flashing and keep the stock firmware on a separate drive.
Official major platform upgrades for this entry‑level model are limited; anticipate security patch support for approximately 18–24 months after launch and occasional incremental feature releases. Check the manufacturer support page for patch history and official changelogs prior to applying any upgrade.
For newer platform releases beyond the official pathway consider community builds (LineageOS, device‑specific ROMs): prerequisites include unlocking the bootloader, installing a custom recovery (TWRP), and flashing a compatible image for the device codename. Preserve the stock ROM for recovery, expect possible loss of vendor optimizations (camera, DRM, VoLTE) and SafetyNet, and recognize the risk of bricking and warranty loss.
Current Android version on Oppo A15s
Check Settings → About phone → Software information to read the installed OS build and security patch level; factory units left the factory with a 10-based core running ColorOS 7. Here’s more info on 1xbet login download stop by our site. 2, while firmware rollouts vary by market and carrier.
How to verify the exact build
Open Settings → About phone and note the entries labeled OS, Build number, Baseband version and Security patch level. Match the model number printed on the box or in About phone with the firmware file name on the vendor support site before taking any action.
How to obtain and apply official firmware safely
Use the vendor’s official support portal or the built-in OTA checker to fetch new firmware/patches. Backup user data, charge the battery above 50%, connect to Wi‑Fi, then install the package via the phone’s Local Install or Recovery flow. Avoid unsigned third‑party ROMs; verify checksums on downloaded packages and follow the vendor’s flashing instructions for your exact model.
Typical support window for this budget handset is one major platform upgrade plus periodic security patches for roughly 12–18 months after release; beyond that, rely only on custom communities and be aware of warranty implications.
Best Android UI Design Tools — Top Apps for Interfaces
Figma delivers browser-based, real-time collaboration, Auto Layout, Variants and reusable components; supports vector networks, constraints and interactive prototypes with smart animate and overlays. Exports include SVG, PNG and PDF; common plugins include Anima, Content Reel and Stark. When you loved this short article and you want to receive more details relating to 1x bet app generously visit our own web-site. Practical setup: create a shared component library, define tokens that cover color, type and spacing, and enable branch-based workflows to isolate iterations.
Sketch remains strong on macOS thanks to Symbols and nested overrides, precise artboards and pixel grid control. Pair with Abstract or Plant to manage branching and version history. Export assets at multiple scale factors (1x, 2x, 3x) and deliver SVG icons suitable for reuse. Licensing uses a paid model with optional update subscriptions; choose Sketch when the workflow is Mac-only and emphasis lies on pixel precision.
Framer and Adobe XD address different needs: Framer focuses on React-driven components and production-ready code exports; Adobe XD integrates with Creative Cloud, offers Auto-Animate and voice triggers plus shared asset libraries. Pick Framer when prototypes require near-production interaction and component code; pick XD when tight Photoshop/Illustrator interoperability is needed.
Practical recommendations: rely on vector assets and SVG icons, export raster images at 1x/2x/3x, embed style tokens as JSON or use a Style Dictionary to sync visual rules with development. Maintain a single source of truth via shared libraries and branching; measure handoff time and reduce repeated asset exports by automating spec generation to PDF or HTML.
Do you mean 10 () sections? Please confirm how many headings you want.
Confirm 10 only if you want exhaustive coverage; my recommendation is 8 headings to keep each part focused and scannable while covering all practical angles.
Suggested section breakdown
1. Quick comparison matrix – one-table snapshot with metrics: learning curve (hours), extensibility, export formats, collaboration features. Target 180–230 words; prep 45–60 minutes.
2. Workflow and prototyping – step-by-step sample project workflow, recommended asset structure, prototype fidelity levels and sample interactions. Target 220–300 words; prep 60–90 minutes.
3. Performance and export workflows – measured render times, recommended export settings, asset compression tips, expected file sizes on release builds. Target 200–260 words; prep 45–75 minutes including benchmark notes.
4. Ecosystem and plugin marketplace – key integrations, must-have plugins, scripting and automation capabilities, compatibility notes. Target 160–220 words; prep 40–60 minutes.
5. Team collaboration and handoff – version control support, commenting and approval flows, role permissions, best practices for developer handoff with spec snippets. Target 200–260 words; prep 60–90 minutes.
6. Learning resources and templates – curated tutorials, official docs, community templates, estimated ramp-up time by skill level (beginner/intermediate/advanced). Target 160–200 words; prep 30–50 minutes.
7. Licensing, pricing models and migration risk – free tier limits, subscription tiers, enterprise extras, migration cost examples (hours and dollars). Target 180–230 words; prep 40–60 minutes.
8. Case studies and sample projects – two short walkthroughs with outcomes: time saved, usability test results, asset weight reduction. Include screenshots list and KPI table. Target 260–350 words; prep 90–120 minutes.
Estimated total length with 8 headings: 1,560–2,100 words and 6–9 hours of research and drafting. If you confirm 10 headings, expect roughly 2,200–3,000 words and 10–14 hours of work, including hands-on tests.
Reply with 6, 8, or 10 to confirm the count and I will return a detailed outline with H2/H3 assignment and per-section bullet points.
Android 9 Name – What Is Android 9 Called? (Android Pie)
Quick facts: this ninth major Google mobile OS release is identified by API level 28, debuted for Pixel phones first on August 6, 2018, and introduced system-level features targeted at power efficiency and modern hardware (display cutouts, multi-camera streams, HEIF image compression).
Key technical changes: gesture-based navigation alternatives to classic buttons; Adaptive Battery (ML-driven background app restrictions); adaptive brightness tuning; official support for display notches; multi-camera API for logical and physical camera combinations; notifications with inline smart replies and image previews; tightened background access to microphone and camera for privacy.
Upgrade checklist: 1) Back up user data and app settings. 2) Charge battery >50% and connect to stable Wi‑Fi. 3) Check your OEM’s update page or device Settings → System → System update for the official OTA. 4) For Pixel devices, factory images and full OTAs are available from Google if manual flashing is required. 5) Verify critical apps for compatibility before committing to the upgrade.
Developer guidance: target and test against API level 28 to validate behavior changes – especially background execution limits, privacy restrictions on sensors and identifiers, and power-management heuristics. Use emulators or physical hardware running version nine to catch runtime differences and ensure libraries are up to date.
Security and lifecycle advice: devices that continue to receive vendor patches on this release remain acceptable for everyday use; devices without active security updates should be replaced or migrated to maintained builds (official vendor firmware or supported custom builds). Check vendor security bulletins and monthly patch availability before relying on an older device.
Official Name and Pronunciation
Use the numeric designation “version 9” (short: v9, API level 28) in documentation; use the dessert moniker only for informal or marketing copy, and indicate its pronunciation when needed.
Pronunciation: single syllable, IPA /paɪ/ (diphthong [aɪ], rhymes with “eye”); stress falls on that sole syllable. Provide /paɪ/ in phonetic guides or captions to avoid ambiguity across accents.
Styling rules: prefer the numeral “9” rather than the spelled-out form in technical contexts – e.g., “version 9 (v9, API level 28)”. In headlines or consumer-facing text, append the dessert moniker after the numeric label and include the phonetic cue in parentheses when first mentioned.
Localization and translation: keep the numeric label untranslated; for the moniker either retain the original term with a local phonetic respelling or use an approved localized equivalent only if officially provided. Always include API level 28 in technical translations to maintain precision.
Legal and usage notes: the dessert moniker is part of the vendor’s marketing assets; verify brand guidelines before using it in third-party materials. For spoken media, instruct narrators to use a steady, single-beat delivery on /paɪ/ rather than stretching the vowel.
Official release name
Use the release identifier “9.0” together with the public dessert moniker “Pie” and API level 28 when labeling this platform version.
- Stable release date: August 6, 2018.
- Primary API level: 28.
- Initial factory build for Pixel family: PPR1.180610.009.
- SDK package: SDK Platform 28 (use platform tools and system images tagged 28 for emulators and CI).
- Runtime and manifest checks: test against Build.VERSION.SDK_INT == 28 and set targetSdkVersion = 28 for compatibility verification.
- Documentation format recommendations:
- User-facing: “9.0 Pie”.
- Technical headers and changelogs: “9.0, API level 28, build PPR1.180610.009” (include security patch level date where relevant).
- Testing checklist:
- Run CTS/GTS or vendor test suites on API 28 system images.
- Validate vendor binaries with the factory build ID listed above.
- Confirm behavior for runtime permissions, gesture navigation, and privacy changes introduced in the 9.0 release.
Should you cherished this article and also you desire to obtain more details regarding 1xbet download pc generously go to the web site.
Which Android Version Does the Redmi 5A Run? — Redmi 5A OS, Updates & Specs
Short answer: Xiaomi 5A shipped with MIUI 9 layered atop Nougat 7. If you’re ready to read more information on 1xbet promo code philippines look into our webpage. 1.2; official firmware provided security patches for roughly two years and did not receive an official platform upgrade to Pie or later. For access to newer platform features and fresher security fixes, choose proven community builds such as Lineage, where unofficial Pie and Q ports exist for this handset.
Key hardware and baseline: Launch: December 2017. SoC: Qualcomm Snapdragon 425 (quad-core Cortex-A53). Memory: 2 GB or 3 GB RAM. Storage: 16 GB or 32 GB with microSD expansion. Display: 5.0-inch HD. Rear camera: 13 MP. Battery: 3000 mAh. Bootloader unlock supported on most regional variants, enabling custom recovery and community firmware installation.
Practical advice: If stability and vendor support matter most, retain official MIUI build and apply security patches when Xiaomi issues them. If need is for newer platform capabilities or longer patch cadence, unlock bootloader, flash a verified custom recovery, then install an actively maintained community ROM compatible with device codename. Always back up user data, verify build signatures and maintainer reputation, and follow step-by-step flashing instructions from reliable sources.
Official Android Version & MIUI on Redmi 5A
Use MIUI 10 Stable (base 7.1.2 Nougat) for balanced feature set and stability; install official Fastboot or Recovery ROMs from Xiaomi servers.
Launch firmware shipped as MIUI 9 on 7.1.2 (Nougat). Xiaomi later rolled MIUI 10 and select MIUI 11 builds for 5A while core platform remained 7.1.2.
Verify current build via Settings > About phone > MIUI build and Kernel/Baseband entries. For official files use MIUI Download page on en.miui.com or fastboot images from Xiaomi servers; match Recovery versus Fastboot package before flashing.
Official security patch cadence concluded around 2019–2020; no official platform upgrade to Oreo (8.x) or newer was provided for 5A.
If a newer core system is required, consider community firmware but expect bootloader unlock, manual flashing, and ongoing maintenance. Follow XDA threads for compatible ports and verify device codename and build compatibility before any flash.
Always backup user data, confirm bootloader status, follow Xiaomi fastboot flashing instructions precisely, and verify ROM checksums prior to applying any firmware change.
Stock Android base and MIUI layer shipped
Recommendation: keep MIUI 9 stable build based on AOSP 7.1.2 (Nougat) for daily use; switch to custom firmware only after unlocking bootloader and a full Nandroid backup.
Concrete layer details and behavior:
- Base: AOSP 7.1.2 (Nougat) with Xiaomi’s MIUI 9 customization.
- Surface changes: custom notification handling, themed system UI, expanded quick settings, bundled system apps (Cloud, Themes, Security, Mi Drop).
- Memory management: aggressive background app killing plus app locking via recent-apps view to preserve processes for chosen apps.
- Permission model: granular runtime permissions similar to AOSP but with extra MIUI permission manager and autostart controls.
- Storage footprint: vendor apps occupy significant internal storage on lower-capacity models; many packages can be removed per user preference.
Practical recommendations for optimization:
- Remove unwanted system apps via ADB to free space and reduce background activity:
adb shell pm uninstall -k --user 0 <package.name>
(replace <package.name> with actual package identifier).
- Disable autostart for apps via Settings > Permissions > Autostart to cut background launches.
- Lock priority apps in recent-apps list to stop MIUI’s aggressive killing for those services.
- Use Security app’s battery and performance tools to whitelist apps that must run continuously.
- For extended lifespan or newer feature set, unlock bootloader with Mi Unlock, install TWRP, then flash Magisk for root or community builds such as LineageOS 14.1/15.1 (verify device-specific support first).
- Always create full Nandroid backup before any bootloader unlock or firmware flash; keep at least one verified backup stored off-device.
Quick risk notes:
- Bootloader unlock may void warranty and requires official Mi Unlock tool plus Mi account authorization.
- Flashing unofficial firmware can break modem compatibility or remove vendor-specific features; verify compatibility and read device threads on active forums before proceeding.
Vivo V15 Android Version – What Android Does It Run? (OS, Specs & Updates)
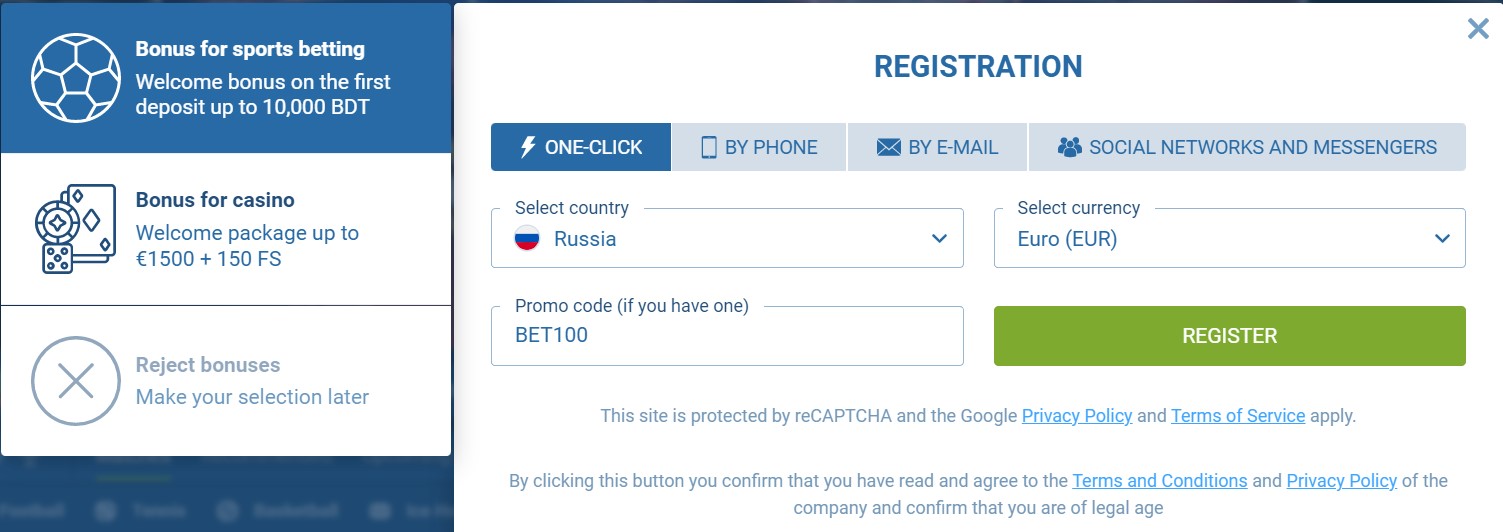
Direct answer: this 2019 V‑series midrange handset left the factory running Google’s Pie (9.0) layered with Funtouch OS 9. If you loved this information and you would certainly such as to obtain even more information regarding 1xbet app ios kindly check out the web site. The device received routine firmware and security patches for roughly the first 12–18 months, while an official rollout of the next major platform generation was limited and not guaranteed for all regional variants.
Practical guidance: check Settings → About phone → System update to confirm the current build and last security patch date. If you require later platform features (Google 10.x/11.x), either contact the device maker for availability or evaluate trusted third‑party builds such as LineageOS–only after verifying an actively maintained build for the device codename, following bootloader unlock steps, and fully backing up user data.
Risk and maintenance checklist: flashing custom firmware voids warranty, may break Widevine/DRM, and can introduce instability; ensure battery >50%, use official flashing tools or documented fastboot procedures, and apply vendor firmware restores if you need to revert. For most users who prioritize reliability and app compatibility, staying on the official Pie/Funtouch release with current security patches is the safest route.
Current Android Version
Install the latest official Funtouch OS 9 build (platform 9 “Pie”) delivered via Settings → System update; if no OTA appears, download the full ROM from the manufacturer support page and flash with the vendor PC tool after a complete backup.
Verify the device’s present build by opening Settings → About phone → Software information: note Build number, Security patch level, Baseband version and the Funtouch entry. Record the exact build string before applying any package or custom firmware.
Prepare the handset for an update: charge to at least 50%, connect to a stable Wi‑Fi network, free 4–6 GB of internal storage, and back up contacts, messages and photos (cloud sync + local export). For app data preservation use the app’s export tools or adb backup for targeted packages.
If the official channel no longer provides major platform upgrades, consider vetted community releases (LineageOS, Pixel Experience) only after confirming device-specific support threads on XDA. Required steps for custom installs: unlock bootloader, install a compatible custom recovery (TWRP), flash vendor firmware blobs if recommended. Expect trade-offs: possible loss of DRM L1, fingerprint or camera quirks and voiding of warranty.
Check Security patch level after any update; if vendor updates cease, switch to a maintained custom build that publishes monthly patch dates. Keep a tested full backup (TWRP nandroid or equivalent) and verified functioning recovery before attempting non-official upgrades.
For everyday use stick to the latest stable official build with current security patches; pursue community firmware only if you accept the technical steps and risks outlined above.
Android version shipped at launch
Shipped with Funtouch 9 layered on 9.0 Pie (stock firmware distributed at market debut in early 2019).
- Base firmware: 9.0 (Pie) with the manufacturer’s Funtouch 9 skin.
- Security patch: typical units carried a patch date from January–March 2019; check Settings → About phone → Security patch for the exact entry.
- Regional/carrier variants: build numbers and preinstalled apps can differ by market – verify the build string under Settings → About phone → Build number.
- How to confirm the shipped build: Settings → About phone → Software information (look for Funtouch release name, base 9.0 and the security patch date).
- Before applying any later firmware packages: back up personal data, connect to a stable Wi‑Fi network, ensure battery ≥50%, then install OTA packages via Settings → System update.
15 Best Little-Known Android Apps — Hidden Gems You Need to Try
This collection highlights 15 under-the-radar mobile utilities for Google’s smartphone platform across productivity, privacy, media and automation. Each entry in the main list includes: install size (MB), last update date, visible permissions, price model (free / freemium / one-time), and a concise one-line use case so readers can pick the right tool for a specific task.
Selection criteria: active maintenance (last update within 12 months), user rating ≥ 4.0 when available, realistic install footprint (preferably <50 MB), minimal access to sensitive permissions (avoid SMS/call access unless clearly justified), and clear data storage policies (local-only or documented cloud processing). Items flagged open-source include a direct repo link where possible.
Quick practical checks before installing: verify the permission list in the store listing, inspect battery usage in system settings after 24 hours, confirm whether backup/export exists, and test any automation rules in a sandbox profile. For network-blocking or VPN-based privacy tools prefer solutions that use a local VPN tunnel without routing traffic through third-party servers; expected CPU impact should remain low (<5% under light load).
The following entries are organized to show immediate value: one-line recommendation, concrete metrics (size, permissions, battery behavior), and the ideal scenario for deployment (offline task management, lightweight media processing, on-device encryption, or automation). Scroll down to find the item that matches a specific workflow and the exact installation footprint for planning storage and data usage.
Offline Notes: Lightweight Markdown Editor
Recommendation: Markor – offline-first, minimal Markdown editor with file-based storage, small footprint (<10 MB), open-source and usable without any network permissions.
- Core capabilities
- Local files: edit .md, .markdown, .txt and todo.txt directly in a chosen folder (internal storage or SD card).
- Live preview and split view: simultaneous editing and rendered output for faster formatting checks.
- Task lists: standard GitHub-style checkboxes (- [ ] / – [x]) with quick toggle support.
- Export & share: HTML export and share-to-print; open notes from any file manager or file mount.
- Small resource use: runs smoothly on low-RAM handsets, negligible battery impact when idle.
- Quick setup (3 minutes)
- Create a dedicated folder (suggestion: Documents/Notes).
- Open Settings → Files → Default directory → select Documents/Notes (permits SD access if needed).
- Settings → Editor → Autosave interval → set 3–10 seconds for fault-tolerant editing.
- Enable Split view in Settings → Viewer for on-device preview while typing.
- Practical templates and snippets
- Meeting note template:
– Date: 2026-03-16
– Attendees:
– Agenda:
– Action items: - Project header (YAML front matter):
—
title: Project X
tags: [project, backlog]
created: 2026-03-16
— - Quick task pattern:
– [ ] Task description @due(2026-03-20) #project
- Meeting note template:
- Search, organization and backups
- Use hashtags (#project, #meeting) and simple filenames (YYYY-MM-DD-meeting.md) for fast filtering with the built-in search.
- Periodic backup: copy the Notes folder to external storage or a mounted WebDAV/Nextcloud folder; an exported ZIP of the folder is handy for periodic snapshots.
- For sensitive content, place the notes folder inside a vault from a file-encryption tool (e.g., Cryptomator) or rely on system-level file encryption.
- Keyboard and workflow tips
- External keyboard shortcuts work: Ctrl+B (bold), Ctrl+I (italic), Ctrl+K (link) for faster composition.
- Create a small set of personal snippets (common headers, signatures) and paste them from the clipboard manager to save repeated typing.
- Use code fences for snippets:
bash
git status
- When to pick this tool
- Prefer Markor when offline-only access, tiny install size and file portability are priorities.
- Consider a sync-capable alternative if encrypted cloud sync and multi-device automatic syncing are required.
Quick start: create a note and sync later
Create a new note, set its sync mode to “Manual” (or mark as local-only), add a UTC timestamp to the filename like 20260316-1430-meeting. If you beloved this article and also you would like to get more info concerning 1xbet registration promo code kindly visit the webpage. md, then save to the local vault or folder. That guarantees a single-file record that can be synced later with no immediate network activity.
Use plain Markdown (.md) or .txt for maximum searchability and smallest file size; keep individual notes under 200 KB for fast uploads. For metadata, include a small YAML frontmatter:
—
created: 2026-03-16T14:30:00Z
modified: 2026-03-16T14:30:00Z
tags: [project-alpha, inbox]
sync: manual
—
Store inline images in a subfolder (attachments/) and reference them with relative paths: . Resize photos to ~1000 px on the long edge and compress to 300–800 KB before attaching to avoid long sync queues. If a rich capture is required, attach a PDF under 10–20 MB; larger binaries delay subsequent syncs.
When offline editing may collide, enable the app’s conflict policy that creates a conflict copy with timestamp and device name, e.g. meeting-notes-conflict-20260316-1530.md. Resolve by opening both files and using a three-way text merge or copy-paste; preserve the earlier file’s created timestamp in the frontmatter where possible.
Recommended sync settings for deferred uploading: set network to “Wi‑Fi only”, enable “Sync on demand” or “Manual sync” and schedule background attempts at 15–30 minute intervals when charging. If background sync is desired, whitelist the note application in the system battery optimizer to prevent kills during long uploads.
Choose a remote host that matches the privacy model: Nextcloud or WebDAV for self-hosting and folder-level control; Dropbox for reliable delta sync; Google Drive for wide availability. For end-to-end encryption, enable the app’s built-in encryption or use a zero‑knowledge provider; keep the encryption passphrase backed up in a separate password manager–losing it means irretrievable notes.
Batch sync process: group related files into one folder, run a manual “Sync now” when on trusted Wi‑Fi, confirm sync log shows successful PUT/UPLOAD for each file, then check timestamps and frontmatter “modified” values. If transfers fail, retry with exponential backoff (15s, 30s, 60s) or switch to manual export of changed files via the share/export feature.
For quick captures from other applications, use the system share sheet to append content to an existing file or create a new note named with a fast prefix like INBOX-20260316.md. Keep inbox files short; triage them into project folders during the next sync session to maintain a clean folder structure: /notes/2026/03/, /projects/project-alpha/.
- Core capabilities
NFC on Android – What It Is, How It Works & How to Use
Enable near‑field communication immediately on your handset: add payment cards to Google Pay, activate reader/writer mode in Settings, and restrict tag access to trusted apps via Permissions → Connected devices. If you have any issues relating to wherever and how to use promo code 1xbet, you can speak to us at our own web-page. For contactless transactions require a secure unlock method (PIN, pattern, biometric) and set your preferred payment application as default to avoid accidental charges.

Technical specifics: operating frequency 13.56 MHz; effective range ~4 cm; supported data rates 106, 212, 424 kbps. Three primary operating modes exist: card emulation (host-based and secure element), peer-to-peer (LLCP), and reader/writer with support for ISO14443 A/B, ISO15693 and FeliCa protocols. Payment implementations rely on tokenization and typically target transaction latency under 300 ms for acceptable user experience.
Enable and verify: navigate Settings → Connected devices → Connection preferences → Near‑Field Communication toggle; confirm functionality by tapping a contactless terminal and checking the transaction entry in Google Pay or device payment history. For field testing, employ a Type A ISO14443 tag and a tag-authoring tool to inspect NDEF records, payload sizes, and access control settings.
Security checklist: keep system firmware current, limit background tag scanning to explicitly permitted apps, disable the radio when idle, enforce device encryption, and remove credentials from lost hardware using Find My Device. Periodically audit installed packages for any host-based card emulation capabilities and revoke privileges granted without clear justification.
Developer notes: target recent API levels in the Google SDK, declare the near‑field communication permission, implement tag discovery with intent filters (ACTION_TECH_DISCOVERED, ACTION_TAG_DISCOVERED), parse NDEF messages, and test against ISO/IEC tag types (Type 2, Type 4). Emulate secure elements only on certified hardware and follow EMVCo tokenization standards when building payment solutions.
Overview: What NFC Means for Android
Require the device’s contactless permission in the app manifest and declare the hardware feature as required when core functionality depends on proximity radio; mark it optional when graceful degradation is acceptable to maximize distribution.
Perform runtime availability checks: query the package manager for the contactless feature flag at startup and gate all related flows behind that check. For payment-style or card-emulation flows, allow them only on API level 19 (KitKat) and above, since host card emulation arrived at that level. Disable peer-to-peer Beam-style transfers for API level 29 and later because that mechanism was removed from the platform.
Prefer the foreground reader-mode API for active tag polling to avoid background intent collisions and to lower false positives. Restrict polling to the exact tag technologies you expect (ISO 14443 A/B, ISO 15693, FeliCa, ISO-DEP) and skip automatic NDEF discovery when you intend raw APDU exchanges; this reduces latency and unnecessary processing. Silence platform sounds for brief sessions when audio feedback would confuse users.
Treat proximity-derived payloads as untrusted input: validate MIME types, enforce maximum NDEF message sizes, reject unexpected record TNFs, and implement strict per-session timeouts. Never store long-term secrets extracted from tags in plain storage; prefer server-side tokenization or a secure element abstraction if hardware-backed keys are required.
Conserve power by activating radio listeners only while the app is foreground-facing and by unregistering callbacks in onPause/onStop. For continuous background monitoring prefer a minimal listener profile and batch processing of reads to limit wakeups. Measure average tag-read latency on target devices and tune polling masks and timeouts to balance responsiveness with battery drain.
Test on a matrix of real tags and readers from multiple vendors, including edge cases: rapid tag removal, partial writes, large multi-record NDEF messages, and ISO-DEP APDU error conditions. Collect telemetry for read/write success rates, exception traces from tag-technology handlers, and frequency of malformed payloads to prioritize fixes before wide rollout.
Define NFC and common Android use cases
Prefer enableReaderMode (API 19+) for tag detection and implement IsoDep + Ndef parsing; for card-emulation flows require HostApduService with tokenization and platform/operator certification, and never store raw card PANs or long-lived secrets on tags or in app storage.
-
Contactless payments:
- Operate at 13.56 MHz with data rates 106 / 212 / 424 kbps; proximity typically ≤4 cm.
- Implement host card emulation (min API 19), process APDUs in HostApduService, integrate with Google Pay or issuer token services; obtain scheme certification before production.
- Security: deploy tokenization, remote provisioning via secure backend, do not write PANs to passive tags.
-
Transit & ticketing:
- Support ISO-DEP (Type 4) and FeliCa for common systems; IDs: ISO14443 UIDs usually 4 or 7 bytes, FeliCa IDm 8 bytes.
- Offline validation often required – implement signed tokens or counters on secure element/HCE; coordinate with operator for key management.
-
Access control & credentials:
- Avoid relying on tag UID alone; implement challenge-response (AES, HMAC) or server-validated ephemeral tokens.
- For lock hardware, prefer ISO-DEP with mutual authentication or SE-backed credentials to prevent cloning.
-
Smart posters & marketing interactions:

- Publish NDEF URI, MIME or Smart Poster records. Keep payloads small (under a few kilobytes) for fastest detection.
- Prefer link shorteners or redirect tokens stored on tag to enable analytics and revocation without rewriting tags.
-
Device pairing and provisioning:
- Implement Bluetooth handover (Handover Request/Select records) or store Wi‑Fi credentials as protected tokens; use the tag only to transfer a small OOB payload that triggers secure setup.
- For large files, trigger cloud transfer rather than embedding binary on tag.
-
Loyalty, coupons, asset tracking:

- Store short IDs or redemption tokens on tags; validate and redeem server-side to allow revocation and reporting.
- Choose tag family by capacity and durability: Type 2 common for small tokens, Type 4/5 for larger records and higher reliability.
-
Peer initiation (handshake only):
- Use short tag exchange to initiate Bluetooth or Wi‑Fi session; deprecated peer-to-peer stack (Android Beam) should be replaced by platform sharing APIs or direct sockets.
- Manifest & hardware: declare android.permission.NFC and
<uses-feature android:name="android.hardware.nfc" android:required="true">if the app cannot operate without reader/emulation. - Discovery strategy: prefer NfcAdapter.enableReaderMode(activity, callback, flags, extras) with reader flags (NFC_A, NFC_B, ISO_DEP, NDEF) and a short timeout; fallback to intent filters only when background dispatch is required.
- Parsing: parse NdefMessage/NdefRecord safely; limit memory allocation to expected payload sizes and validate MIME types and record counts before processing.
- Emulation: implement HostApduService for card-emulation flows, provide metadata in manifest and ensure APDU timing/response sizes match payment/transport specs.
- Testing & hardware: verify with NTAG21x, MIFARE Ultralight, Type 4 ISO‑DEP tags and a contactless reader (ACR122, PN532) across cases and phone models; test with phone cases and metal surfaces that degrade coupling.
- Security checklist: never store long-lived secrets on passive tags, enable backend validation, rotate keys/tokens, log failed attempts and implement rate limiting on server side.
Tag selection quick reference: Type 2 – common small capacity (≈48 bytes–2 KB), Type 4 – ISO‑DEP with larger payloads and faster compatibility, Type 5 – ISO15693 for extended range and larger memory (several KB+). Match expected payload, read/write cycles and tamper resistance to the application requirements.
-
Vivo Y19 Android Version – What Android OS Does It Run?
Check current software: open Settings → About phone → Software information and note Build number, Baseband version and Security patch level. Use Settings → System updates (over Wi‑Fi) to fetch the official package. Back up contacts, photos and a full system backup to external storage or cloud before any upgrade.
Official update path: download the firmware that exactly matches your model code from the manufacturer’s support portal, verify the file’s SHA256 checksum, then apply via Settings → Local update or the stock recovery. Keep battery above 50% (charger connected preferred) and at least 2 GB free storage for the package.
When there is no official upgrade: contact support to confirm roadmap. If you need newer features from Google mobile OS 10/11, research community builds on developer forums for your exact model codename; expect missing vendor drivers, potential camera and fingerprint regressions, and the need to unlock the bootloader (which voids warranty).
Quick checklist: 1) Backup data; 2) Confirm model code and download correct firmware; 3) Verify checksum; 4) Ensure battery ≥50% and stable connection; 5) Follow stock updater or recovery procedure; 6) Avoid unverified packages and always keep a copy of original firmware.
Current Official Android Version
Officially the handset ships with Google’s mobile OS 9 (Pie) layered with Funtouch OS 9.2; there has been no official major platform upgrade released for this model, only occasional security-patch updates.
Verify the installed software: open Settings > About phone > Software information and note the OS entry, build number and security patch level. Save the build number before applying any update or custom firmware.
To receive official over-the-air updates: connect to a stable Wi‑Fi network, ensure battery is above 50%, back up user data, then go to Settings > System update (or Software updates) and tap Check for updates. Install only updates delivered through the phone’s updater or the manufacturer’s support portal.
If no update is offered but you need a newer patch, download the official firmware for your model from the manufacturer support site using the device code or IMEI. Follow the vendor’s flash instructions or visit an authorized service center for assistance.
For users considering aftermarket firmware: custom ROMs (e.g., LineageOS builds) can provide later platform releases, but require an unlocked bootloader, model-specific builds and technical experience. Flashing third-party images voids warranty and carries data-loss and security risks; consult established device forums and follow step-by-step guides with verified checksums.
Factory Android release and Funtouch OS version
Factory configuration: shipped with Pie (9.0) as the base platform paired with Funtouch OS 9.2; apply the latest official OTA for security patches and stability fixes rather than third‑party builds.
Verify current build: open Settings → About phone → Software information to read Base OS (Pie 9.0), Funtouch OS entry and Build number; check Kernel version date and Android security patch level for patch recency. Use Settings → System update (or Software update) to look for official updates.
Update checklist: back up all user data; charge battery to at least 50% (80% recommended); connect to a stable Wi‑Fi network; free 3–5 GB internal storage; disable aggressive power saving during the process. Should you adored this information along with you wish to obtain more details concerning 1xbet promo code for free bet kindly stop by the internet site. If OTA isn’t offered and you must flash manually, download the official firmware for your exact model/region from the manufacturer’s support site and verify checksums before flashing.
Flashing and rollback notes: manual installation or unlocking the bootloader can void warranty and will erase user data – export IMEI/EFS/NV backups if possible. If unsure, use authorized service or follow the vendor’s step‑by‑step guide to avoid bricking the device.
Current Android Version – What’s the Latest Android Version Now?
Quick recommendation: Update devices that support release 14 (API 34) to receive security fixes, privacy enhancements, and UI refinements.
Release details: Official stable rollout began October 4, 2023. Build targets API level 34. If you have any kind of concerns pertaining to where and the best ways to make use of promo code 1xbet, you can contact us at our own page. Major changes include per-app language preferences, expanded lockscreen widgets and customization, stricter background permission rules, optimized memory handling for large displays, improved accessibility magnification and font scaling, and stronger passkey support for passwordless sign-ins.
Security and maintenance: Monthly security patches continue; vendors distribute updates on staggered schedules. For fastest delivery choose a Pixel device or carrier-unlocked handset with active vendor support.
How to prepare: Create a full backup via cloud or local image; charge battery above 50%; connect to stable Wi‑Fi; free at least 3 GB storage; review app compatibility notes from app developers before applying update.
If update isn’t available: Check OEM support pages, enroll in official beta or security programs only from trusted vendors, or consider switching to a handset with longer update commitment.
Action now: Prioritize devices that handle sensitive data for immediate upgrade; postpone update on mission-critical hardware until app and vendor compatibility are verified.
Check Your Device’s Android Version
Verify OS release and security patch monthly: open Settings > About phone > Software information.
Locate OS release number (example: 13, 12), API level, Build ID and Security patch level under Software information.
Samsung path: Settings > About phone > Software information. Pixel / OnePlus / Xiaomi path: Settings > System > About phone.
Record Build ID and Security patch date before installing updates; back up user data via Settings > System > Backup or vendor cloud.
When an update appears: use Wi‑Fi, charge battery above 50%, connect device to power, allow install to complete without interruption.
For deeper inspection, install a device‑info utility such as “CPU‑Z” or “Device Info HW” from Play Store; open app and check OS release, API level, Build ID and Security patch fields.
If updates are missing from Settings, search vendor support pages with device model and Build ID to find matching OTA or factory image; apply only files meant for exact model/build.
Open Settings and locate About phone
Open Settings and tap About phone (or About device) to view OS release, build number, security patch level, kernel information and update status.
-
Open Settings: tap the gear icon from the app drawer or pull down Quick Settings and tap the gear.
-
Use the built-in search: type “About” to jump directly to the correct screen if the menu is deep.
-
Common menu paths (select the matching UI):
- Stock/Pixel-style: Settings > System > About phone.
- Samsung One UI: Settings > About phone > Software information.
- MIUI (Xiaomi/Redmi): Settings > About phone > All specs or MIUI version / OS release.
- OxygenOS (OnePlus): Settings > About phone > Version information.
- EMUI (Huawei): Settings > About phone > Software information.
-
If labels differ, look for “About”, “Software information”, “All specs” or “Device info”. Older skins may list About under General or System.
-
To reveal build number for developer options: tap Build number seven times on the About screen (watch for a countdown toast).
Quick checklist – copy or note these fields from About phone:
- OS release (named “OS release”, “OS build” or similar)
- Build number
- Security patch level
- Kernel version
- Baseband/modem or firmware version
- Model number and IMEI (if needed)
-

