How to Recover Deleted Files on Android – Complete Step-by-Step Guide
Immediate recommendation: enable Airplane mode and stop adding new media or documents to the device to minimize overwrite risk; if possible, power the device down and remove any external SD card before any further action.
Cloud check first: inspect Google Photos Trash (items retained for 60 days), Google Drive Trash (30 days), your OEM cloud (Samsung Cloud, OnePlus backup) and any third‑party sync (Dropbox, OneDrive). Restoring from cloud copies is fastest and avoids any scans that write to internal storage.
If no cloud copy exists, extract the removable card and attach it to a PC via a card reader; run a sector‑level imaging tool (dd, Win32 Disk Imager) to create a raw image, then run PhotoRec or DMDE on the image rather than the original card. For internal flash, enable Developer Options → USB debugging and use adb to pull user folders (/sdcard/DCIM, /sdcard/Pictures) to a local drive before attempting deeper scans.
Choose recovery software based on access level: non‑root tools (DiskDigger, PhotoRec) can restore many media types without elevated privileges; root‑level utilities (Undeleter, Tenorshare UltData, Dr.Fone with root) allow raw partition access and higher success rates but may void warranty or trigger security wipes. Prefer PC utilities that scan an image file rather than installing apps on the subject device.
Order of operations: 1) cloud restore, 2) card imaging + PC scan, 3) image-based scan of internal storage, 4) vendor restore tools, 5) professional lab if data value is high. Keep records of each attempt, avoid firmware updates or factory resets, and if data integrity is critical, stop and consult a specialist rather than performing risky procedures yourself.
Initial assessment and quick precautions
Stop all write activity now: turn on Airplane mode, disable Wi‑Fi and mobile data, stop camera and syncing apps, and avoid creating new photos, messages or downloads.
Remove external storage: eject any microSD card and keep it aside in an anti‑static sleeve. Use a USB card reader to access the card from a PC for imaging rather than using the phone.
Check cloud trash and backups immediately: open Google Photos Trash at https://photos.google.com/trash (items remain up to 60 days for media), and Google Drive Trash at https://drive.google.com/drive/trash (items auto‑deleted after 30 days). Inspect OneDrive, iCloud (if applicable) and any OEM cloud accounts for recent snapshots.
Record device metadata: note model, build number and Android version from Settings > About phone. Capture the timestamp of the last automatic backup: Settings > Google > Backup (or Settings > Accounts and backup on some OEMs). Save screenshots or photos of these screens on a separate device.
Do not install recovery apps on the handset: installing helpers or utilities to internal storage causes writes that lower the chance of restoring lost data. If you must run a utility, do it from a PC and access the phone in read mode.
If USB debugging is already enabled: attach the phone to a trusted PC and run adb pull /sdcard/ ~/phone_backup to copy user storage. Do not enable USB debugging if it was off: that changes system state and can overwrite data.
Image removable storage before any attempts at restoration: on Linux, use dd if=/dev/sdX of=~/sdcard.img bs=4M conv=sync,noerror (replace /dev/sdX with the reader device). Verify image integrity with sha256sum of both source and image.
Avoid rooting or factory resets: rooting may trigger background writes; a factory reset will wipe partitions and remove any chance of later retrieval. If internal storage imaging is required, prefer a specialist lab unless you have forensic tools and experience.
Check app‑specific backups next: WhatsApp: Settings > Chats > Chat backup (note backup date and whether Google Drive backup exists); Telegram: confirm cloud messages via desktop client; camera apps or third‑party galleries may maintain their own trash folders–inspect each app’s settings and “recent” or “trash” sections.
Document every action: keep a timestamped log of steps taken, connections made and tools used. That log helps avoid repeated writes and supports professional help if escalation is needed.
Identify exact file types and locations deleted
Create an inventory of MIME types and absolute paths before performing any write operations on the storage.
Common extensions to list and search for: images – .jpg, .jpeg, .heic, .png; video – .mp4, .mov, .3gp; audio – .mp3, .m4a, .wav; documents – .pdf, .docx, .xlsx, .pptx; archives and packages – .zip, .rar, .tar, .apk; databases and app stores – .db, .sqlite; thumbnails – .thumb, .thm. Also include hidden names starting with a dot (.). Record expected MIME types (image/jpeg, video/mp4, application/pdf, etc.).
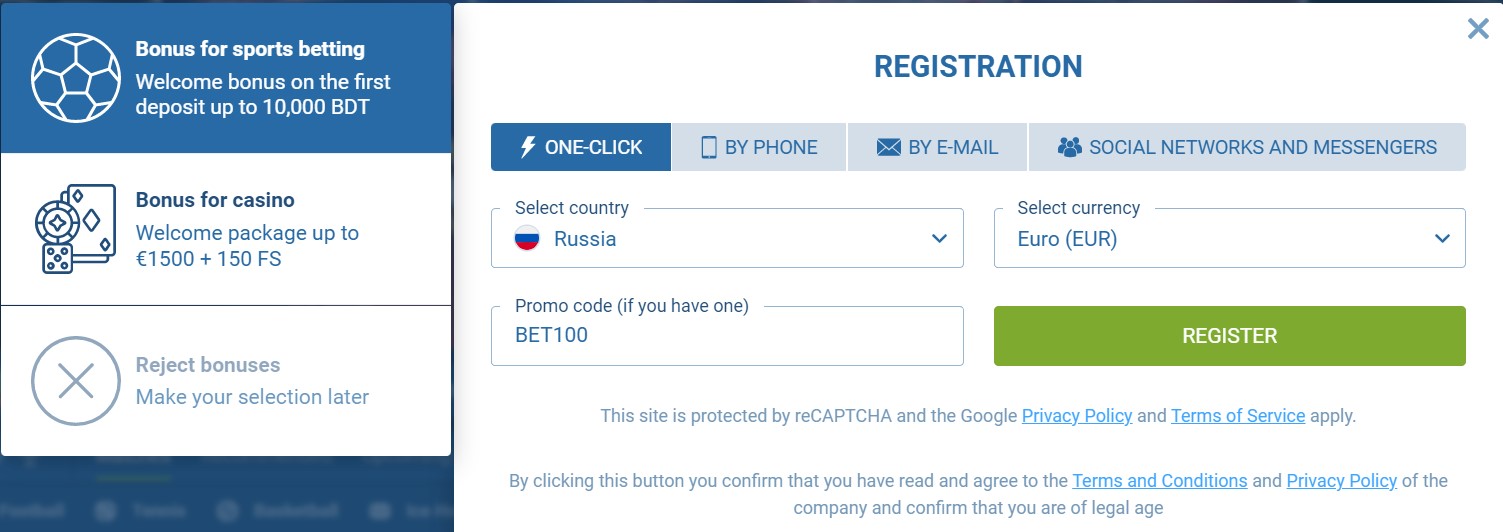
Typical user-accessible paths to check (use exact spelling when querying): /storage/emulated/0/DCIM/Camera; /storage/emulated/0/Pictures; /storage/emulated/0/Movies; /storage/emulated/0/Music; /storage/emulated/0/Download; /storage/emulated/0/DCIM/.thumbnails; /storage/XXXX-XXXX/ for SD card mounts. App-specific locations: /storage/emulated/0/WhatsApp/Media/WhatsApp Images and /WhatsApp/Databases; /storage/emulated/0/Telegram/; /storage/emulated/0/Android/media//; /storage/emulated/0/Android/data// (app cache and data). If you cherished this post and also you would like to be given more info concerning download 1xbet app kindly stop by the web page. System-only area: /data/data//databases (root required).
Use exact-match strategies rather than broad scans: search by extension plus size and timestamp ranges. Example quick queries via adb (device must allow debugging): adb shell ls -R /storage/emulated/0 | grep -Ei ‘\.(jpg|jpeg|heic|png|mp4|mov|mp3|pdf)$’ and adb shell find /storage/emulated/0 -type f -iname ‘*.jpg’ -printf ‘%p %s %TY-%Tm-%Td %TH:%TM:%TS
‘.
Verify type by magic bytes and metadata, not only by extension: pull a sample with adb pull and run file –mime-type sample on your workstation, or run exiftool -j sample to read EXIF dates and camera model. For databases, use sqlite3 to inspect schema and tables (sqlite3 sample.db ‘.tables’).
Query the media index to map original locations and timestamps (root may be required for direct DB access). Example: adb shell cmd content query –uri content://media/external/file –projection _data,mime_type,_size,date_added –where “mime_type=’image/jpeg'”. For direct DB: sqlite3 /data/data/com.android.providers.media/databases/external.db “SELECT _data,mime_type,_size,date_added FROM files WHERE _data LIKE ‘%DCIM%’;”
Correlate metadata fields to pinpoint exact target: match date_added/date_modified and _size from MediaStore to a candidate item on storage; compare checksum (md5sum) of any thumbnail in /DCIM/.thumbnails with a retrieved blob to confirm identity before further actions.
Check cloud and app backups next: Google Drive/Photos, OneDrive, Dropbox, and service-specific backup files (example: WhatsApp local backups under /WhatsApp/Databases/msgstore*.crypt12 and corresponding cloud backups). Export app export or backup lists where available and compare timestamps and sizes to local inventory.
Export a snapshot of the current media index to CSV to prioritize targets: adb shell sqlite3 /data/data/com.android.providers.media/databases/external.db “SELECT _id,_data,mime_type,_size,date_added FROM files;” > media_index.csv, then filter by directory, extension, size and date to produce a precise retrieval plan.
How to Recover Deleted WhatsApp Chats on Android — Step-by-Step Guide
Immediate action: if a cloud snapshot exists, uninstall then reinstall the messenger and select the restore from Google Drive option using the same Google account and phone number; the app will detect the latest cloud backup and apply it during setup. If no cloud snapshot is available, locate the latest msgstore-YYYY-MM-DD.1.db.crypt12 (or msgstore.db. If you adored this article and you would like to collect more info pertaining to 1xbet code kindly visit our web-site. crypt12) file in the messenger’s Databases folder on internal storage, copy it to the device root, rename to msgstore.db.crypt12, then reinstall the app to trigger a local restore. Use USB MTP or adb pull if direct file access is needed.
Cloud snapshots are tied to a Google account and the phone number registered in the messenger; they are created automatically (daily by default, around 02:00 local time) and the app shows the backup timestamp in Settings → Backups. Local copies are generated each night and the client retains a rolling set (typically seven daily files). If end-to-end backup encryption was enabled, you must supply the backup password or encryption key during restore – without it the archived database remains unreadable.
Third-party recovery utilities can attempt deeper file-level extraction, but use them only after exporting critical threads via the app’s “export conversation” option (email or cloud) and after verifying the tool’s reputation and permissions. To reduce future risk, enable daily cloud snapshots, keep local backups intact during transfers, and periodically export any high-priority message threads to a separate archive outside the messenger.
Verify WhatsApp Backup and Account
Confirm Google Drive backup timestamp immediately: open drive.google.com (desktop) or the Drive app → Menu → Backups; locate the backup entry corresponding to your account/phone number and verify the “Last backup” date is after the messages you need and the size is not zero (typical non-empty backups are >100 KB).
Check on-device local backup files: use a file manager to open internal storage → the messaging-app folder → Databases; verify presence of files named msgstore-YYYY-MM-DD.1.db.crypt12 (or similar crypt version), confirm the file modification date and that file size aligns with expected history.
Ensure identical phone number and account: confirm the phone number shown in the app’s Account section matches the SIM number on the device; verify the Google account used for Drive backups is the same account currently signed in under device Accounts → Google.
Verify backup encryption settings and key availability: if encrypted backups are enabled, make sure you have the 64-digit key or the chosen password stored offline; without that key/password the encrypted backup is unreadable. Check the app’s Backup options to see whether end-to-end encrypted backups were activated and export or record the key now if possible.
Confirm Drive permissions and Play Services status: open device Settings → Apps → Google Play services and ensure Play Services is enabled and up to date; in Google Account permissions (myaccount.google.com/permissions) confirm the messaging app has Drive access. Revoke and re-grant Drive access only if the backup entry still does not appear.
Compare timestamps and sizes before any reinstallation: if the local msgstore file is newer than the Drive entry, make a manual copy of that file to a safe folder (and to a computer) before taking further steps; if Drive is newer, confirm network stability and that the device is signed into the same Google account used to create that Drive backup.
Create an immediate manual backup: trigger an in-app manual backup to Drive and verify the new timestamp both in the Drive Backups list and in the local Databases folder; keep battery above 40% and use Wi‑Fi to avoid interrupted uploads.
Check Google Drive backup date
Open the Google Drive app → menu (three lines) → Backups; on desktop go to drive.google.com/drive/backups. The backup list shows entries for device and app backups with a “Last backup” timestamp and size.
Tap the messaging-app entry to view detailed metadata: exact date/time, backup size, and which components were included (media or messages). On web, click the backup row to reveal the same fields.
Compare the “Last backup” timestamp to the moment content was removed. If the timestamp is earlier than that moment, the backup will not contain newer items; if it is later, the copy should include them.
If the displayed time looks unexpected, confirm device clock and account timezone: Settings → System → Date & time → use network-provided time. Drive timestamps may appear in UTC or the account’s timezone, so adjust your comparison accordingly.
No backup entry visible for the messaging app? Refresh the Drive app (pull-to-refresh) and check a second Google account if multiple are present (tap profile icon). Also confirm available Drive storage – a full quota can block scheduled backups.
If the timestamp matches the period you need, reinstall the messaging app from Play Store, register with the same phone number and Google account, and accept the restore prompt when offered; the restore will use the Drive backup with that timestamp.
What Is an Android Device? Definition, Features & Examples
Pick a model running Google’s open-source mobile operating system if you need the largest app catalog, wide hardware choice and deep customization. If you loved this short article and you would like to get far more details about 1xbet apk kindly take a look at the web page. Target units with 64-bit ARM (ARMv8-A/ARM64) SoCs, 4–12 GB RAM, and UFS 2.1+ storage to avoid bottlenecks in multitasking and media processing.
Market footprint: the Google mobile platform accounts for roughly 70–75% of active smartphones globally (StatCounter, 2023). The official app marketplace hosts over 2 million apps; sideloading is supported on most builds, enabling alternative stores and direct APK installs. Google publishes monthly security patches, while manufacturer OS-update policies typically range from 2 to 5 years–check vendor commitments before purchase.
Supported form factors include phones, tablets, smartwatches (Wear OS), smart-TV builds (Google TV), in-car infotainment, and low-power IoT modules. Notable capabilities: split-screen multitasking, per-app permission controls, biometric unlocks (fingerprint/face), hardware-accelerated codecs (HEVC, AV1 on modern chips), and broad modem support for LTE and 5G NR sub-6GHz bands.
Recommended choices by priority: for fastest updates and compatibility with privacy-focused forks choose Pixel-series hardware; for extended OEM support and advanced camera systems choose Samsung Galaxy flagships; for value-oriented performance consider OnePlus, Xiaomi, OPPO or Realme flagships. If you plan custom firmware, verify bootloader unlock policy, vendor kernel sources and baseband firmware availability; for hardened privacy builds favor devices with strong upstream kernel support and vendor cooperation.
Practical definition of an Android device
Verify platform identity immediately by performing these checks on the unit:
-
ADB connectivity and basic properties
- Connect via USB and run:
adb devicesto confirm a connection. - Read key system properties:
adb shell getprop ro.product.manufacturer,adb shell getprop ro.product.model,adb shell getprop ro.build.fingerprint,adb shell getprop ro.build.version.sdk,adb shell getprop ro.build.version.release. - Interpretation: manufacturer/model show vendor; fingerprint indicates stock vs custom signing; SDK number gives API level.
- Connect via USB and run:
-
Inspect build files
- Open
/system/build.propor/vendor/build.prop:adb shell cat /system/build.prop | grep -E "ro.product|ro.build". - Values to note:
ro.build.tags(containsrelease-keysfor vendor-signed ROMs,test-keysfor custom),ro.build.type(user/userdebug/eng).
- Open
-
Bootloader and fastboot checks
- Reboot to bootloader and run:
fastboot getvar allor vendor-specific:fastboot oem device-info. - Confirm lock state (locked = vendor-protected; unlocked = custom ROM or unlocked bootloader).
- Reboot to bootloader and run:
-
Kernel, SELinux and verified boot
- Check kernel build:
adb shell uname -a. - Check SELinux mode:
adb shell getenforce(returns Enforcing or Permissive). - Check verified boot state:
adb shell getprop ro.boot.verifiedbootstateoradb shell getprop ro.boot.vbmeta.digest; look for vendor-signed verification flags.
- Check kernel build:
-
App ecosystem and services
- List installed packages:
adb shell pm list packages. - Search for Play Store / Play Services indicators:
adb shell pm list packages | grep -Ei "play|gms|google". Presence indicates Google Mobile Services integration; absence suggests a Google-free build.
- List installed packages:
-
Hardware identifiers and ABI
- Get CPU ABI:
adb shell getprop ro.product.cpu.abiandadb shell getprop ro.product.cpu.abilist. - Inspect
/proc/cpuinfofor core count and architecture.
- Get CPU ABI:
-
Security flags and debug status
- Check
ro.debuggableandro.secureviaadb shell getprop. Debuggable=1 or secure=0 indicates non-production build. - Check for root binaries:
adb shell which suoradb shell ls /system/xbin/su.
- Check
Quick checklist for classification:
- Fingerprint contains
release-keys+ locked bootloader + Play ecosystem present = vendor-stock handset. - Fingerprint contains
test-keysoruserdebug/eng, unlocked bootloader, debuggable=1 = custom build or engineering image. - SELinux=Permissive, root binary present = compromised or developer-flash image.
- API level number identifies OS generation; map SDK number to release number when needed.
Use the commands and property checks above as a reproducible checklist for inventorying, support triage, forensics, or build verification.
Core components that make a device “Android”
Deploy a certified system image that includes a mainline Linux kernel with a binder driver, verified boot (dm-verity or vbmeta), SELinux in enforcing mode, and a hardware-backed keystore (TEE/StrongBox) before accepting builds for production.
Kernel and low-level drivers: binder IPC, ashmem or shared-memory support, dma-buf for buffer sharing, display HWC, audio HAL, power management (wakelocks/pm), and GPU drivers must be present and upstream-friendly where possible. Provide device trees and dtb for SoC-specific initialization and ensure kernel configuration enables CONFIG_SELINUX and CONFIG_ANDROID_BINDER.
Runtime and app packaging: include the ART runtime with support for ahead-of-time (AOT) and JIT compilation, dex2oat toolchain, and package handling for APK and app bundles (.aab). Implement signature verification using APK Signature Scheme v2/v3 and support runtime permissions introduced at API level 23.
Framework and services: system_server processes exposing ActivityManager, WindowManager, PackageManager, Location, Telephony and Notification services; Java/Kotlin framework APIs consistent with the target SDK level; Binder-based service bindings; and a robust package manager that enforces install-time and runtime permission policies.
Vendor interface and partitioning: separate vendor implementations via HIDL/AIDL or VINTF to allow OS upgrades without vendor modifications. Standard partition layout should include boot, system/product, vendor, odm, recovery and userdata. Support Treble-style vendor separation to simplify OTA delivery.
Security primitives: Verified Boot with rollback protection, file-based encryption (FBE) and/or full-disk encryption, SELinux labels for processes and files, hardware-backed attestation, secure boot chain, and support for safety/attestation APIs. Maintain up-to-date CVE patches and implement secure default settings for adb and network debugging.
Update and recovery mechanisms: supply an OTA pipeline that supports A/B (seamless) updates or robust recovery-based updates, signed update payloads, delta patching to minimize download size, and a reliable recovery image with fastboot-compatible flashing.
Tooling and developer interfaces: include adb, fastboot, logcat, dumpstate, and package management tools; expose proper vendor and framework logs for debugging while keeping production builds with restricted debug access and verified release keys.

-
Fix Android Phone That Can’t Enter Menu — Quick Troubleshooting Guide
If the home screen or app list is unresponsive, a forced reboot resolves kernel hangs on most Google-based mobiles. Try Power + Volume Down for 10–12 seconds; if no result try Power + Volume Up for 10 seconds or Power + Home for models with a physical home key. For devices with removable batteries, remove battery for 30 seconds then reinsert.
Boot into safe mode to isolate third-party apps: press and hold Power until power options appear, then press and hold the on-screen power-off option until a prompt to reboot into safe mode appears, confirm to boot. While in safe mode only preinstalled applications run; if the options panel works, uninstall recent installs from the last 48–72 hours and revoke accessibility or overlay permissions for suspect apps.

Clear launcher data before a full reset: open Settings → Apps → Show system apps, locate your launcher (for example Pixel Launcher, One UI Home, Nova Launcher) and choose Storage → Clear cache. If clearing cache does not help, use Clear data / Clear storage but note this resets home layout and shortcuts; export launcher settings or photograph key screens first.
Backup before proceeding: copy contacts, photos and app data to cloud storage or to a PC. Perform a factory erase from system: Settings → System → Reset options → Erase all data (factory reset). To use recovery mode: power off, press Power + Volume Up (model-specific), navigate with volume keys to “Wipe data/factory reset” and confirm with Power. For suspected firmware corruption consider reflashing the stock image using vendor tools (Odin for Samsung, Fastboot for many manufacturers).
Suspect hardware failure if touchscreen response is partial, buttons are erratic or the device repeatedly reboots. In those cases contact an authorized repair center or the manufacturer. For advanced diagnostics capture logs via ADB (adb logcat, adb bugreport) and match the build number against vendor advisories before attempting firmware reflash.
Quick Pre-checks
Reboot using a forced restart: hold the power and volume-down keys simultaneously for 12–15 seconds until the unit reboots; if no response, hold for up to 30 seconds.
Check battery and charger: confirm battery level above 10%; use the original charger or a 5V/2A rated adapter and a known-good cable; verify charging indicator or on-screen animation within 2 minutes of connection.
Inspect hardware keys and ports: press each physical button to confirm actuation, remove the case, clear visible debris, and blow out headphone and USB-C openings with low-pressure canned air; avoid inserting metal objects.
Test touchscreen and display: perform full-screen swipes across all edges; connect an external USB mouse via an OTG adapter to verify pointer control; if mouse input works while touch does not, the digitizer may be defective.
Boot to Safe Mode to check for app interference: power off, power on, and when the vendor logo appears hold volume-down until a Safe Mode indicator is visible; confirm whether the system options list becomes accessible in that state.

Verify storage and cache: ensure at least 1 GB of free space; clear app caches from settings or remove large media files to free space, since under 500 MB often causes UI freezes or slowdowns.
Review recent installs and updates: open settings > apps, sort by install date or battery usage, and uninstall or disable apps added within the last 48 hours to isolate problematic software.
If the interface remains unresponsive after all checks, boot to recovery and perform a cache-partition wipe only: power off, use the vendor-specific key combo to access recovery, select “wipe cache partition,” then reboot; avoid factory reset unless data is backed up.
Restart the phone and try opening the menu
Perform a soft restart: press and hold the Power key for 10–15 seconds until the display goes dark, release, wait 30 seconds, then press Power to boot. This clears stalled processes and frees RAM, often restoring responsiveness for the app drawer and system UI.
If the unit is frozen, perform a forced reboot using key combinations: hold Power + Volume Down for 8–12 seconds; if no reaction try Power + Volume Up for 8–12 seconds. Consult the manufacturer’s support page for model-specific sequences.
For models with a removable battery, remove the battery for 10–15 seconds, reinsert, and power on. For sealed units, avoid disassembly and use forced-reboot combos instead.
After reboot, open the app drawer or launcher and test navigation. If icons remain unresponsive, boot into safe mode to isolate third-party launcher or app interference: press and hold Power until power options appear, then long-press “Power off” and accept the Safe Mode prompt; on some models hold Volume Down during boot. While in safe mode, test the app list and uninstall recent apps or switch launchers as needed.
If safe mode doesn’t restore the app list, clear the cache partition via recovery: power off, hold Power + Volume Up (add Home on older models) until recovery appears, use Volume keys to highlight “wipe cache partition”, press Power to confirm, then reboot. If you loved this short article and you would certainly like to obtain more details concerning 1xbet login ph kindly check out the web site. Cache wipe preserves personal files.

If issues persist after cache wipe and safe mode, back up photos, contacts, and app data, then perform a factory reset from Settings > System > Reset options > Erase all data (factory reset) or via recovery using “wipe data/factory reset”. After reset, test the launcher before restoring all apps; reinstall only essential apps first.
After stable behavior returns, check for system updates (Settings > System > Software update) and update the launcher through the app store to reduce recurrence.
Vivo V15 Android Version – What Android Does It Run? (OS, Specs & Updates)
Direct answer: this 2019 V‑series midrange handset left the factory running Google’s Pie (9.0) layered with Funtouch OS 9. If you loved this information and you would certainly such as to obtain even more information regarding 1xbet app ios kindly check out the web site. The device received routine firmware and security patches for roughly the first 12–18 months, while an official rollout of the next major platform generation was limited and not guaranteed for all regional variants.
Practical guidance: check Settings → About phone → System update to confirm the current build and last security patch date. If you require later platform features (Google 10.x/11.x), either contact the device maker for availability or evaluate trusted third‑party builds such as LineageOS–only after verifying an actively maintained build for the device codename, following bootloader unlock steps, and fully backing up user data.
Risk and maintenance checklist: flashing custom firmware voids warranty, may break Widevine/DRM, and can introduce instability; ensure battery >50%, use official flashing tools or documented fastboot procedures, and apply vendor firmware restores if you need to revert. For most users who prioritize reliability and app compatibility, staying on the official Pie/Funtouch release with current security patches is the safest route.
Current Android Version
Install the latest official Funtouch OS 9 build (platform 9 “Pie”) delivered via Settings → System update; if no OTA appears, download the full ROM from the manufacturer support page and flash with the vendor PC tool after a complete backup.
Verify the device’s present build by opening Settings → About phone → Software information: note Build number, Security patch level, Baseband version and the Funtouch entry. Record the exact build string before applying any package or custom firmware.
Prepare the handset for an update: charge to at least 50%, connect to a stable Wi‑Fi network, free 4–6 GB of internal storage, and back up contacts, messages and photos (cloud sync + local export). For app data preservation use the app’s export tools or adb backup for targeted packages.
If the official channel no longer provides major platform upgrades, consider vetted community releases (LineageOS, Pixel Experience) only after confirming device-specific support threads on XDA. Required steps for custom installs: unlock bootloader, install a compatible custom recovery (TWRP), flash vendor firmware blobs if recommended. Expect trade-offs: possible loss of DRM L1, fingerprint or camera quirks and voiding of warranty.
Check Security patch level after any update; if vendor updates cease, switch to a maintained custom build that publishes monthly patch dates. Keep a tested full backup (TWRP nandroid or equivalent) and verified functioning recovery before attempting non-official upgrades.
For everyday use stick to the latest stable official build with current security patches; pursue community firmware only if you accept the technical steps and risks outlined above.
Android version shipped at launch
Shipped with Funtouch 9 layered on 9.0 Pie (stock firmware distributed at market debut in early 2019).
- Base firmware: 9.0 (Pie) with the manufacturer’s Funtouch 9 skin.
- Security patch: typical units carried a patch date from January–March 2019; check Settings → About phone → Security patch for the exact entry.
- Regional/carrier variants: build numbers and preinstalled apps can differ by market – verify the build string under Settings → About phone → Build number.
- How to confirm the shipped build: Settings → About phone → Software information (look for Funtouch release name, base 9.0 and the security patch date).
- Before applying any later firmware packages: back up personal data, connect to a stable Wi‑Fi network, ensure battery ≥50%, then install OTA packages via Settings → System update.
How to Connect AirPods to Android – Easy Step-by-Step Guide

Immediate action: Place both buds into the charging case, open the lid, press and hold the rear setup button until the status LED flashes white (≈2–5 seconds). On the phone (phones running Google’s mobile OS 6.0+ with Bluetooth 4.0+), open Settings → Bluetooth, enable Bluetooth, wait for the earbuds’ name to appear (often “Owner’s name Earbuds”) and tap it; pairing usually finishes in 1–3 seconds and shows as “Connected” for media and calls.
If pairing does not complete, delete any prior pairing entry for those earbuds from the phone’s Bluetooth list, disable Bluetooth on nearby devices that might interfere, ensure the case and buds have at least 30% charge, then retry. To reset to factory pairing state: with the case lid open press and hold the setup button ~15 seconds until the LED briefly flashes amber then white, then run the pairing sequence again. Grant location permission when prompted – Bluetooth scanning on Google OS often requires it to discover nearby devices.
Practical notes: Expect standard SBC audio; AAC playback may work on some handsets but can add latency. Apple-exclusive integrations (instant device switching, pop-up battery cards, firmware updates) require an Apple device and will not be available on a Google-OS phone. Microphone for calls, ANC/Transparency on Pro models and basic controls function, but gesture remapping and battery readouts typically need third-party apps such as AirBattery or Assistant Trigger. For firmware updates and full feature control, use an iPhone or iPad.
Prepare your Android device
Open Settings → Bluetooth and keep the Bluetooth screen visible during the pairing attempt; many phones stay discoverable while that page is open (≈2 minutes).
Confirm system and radio compatibility: run Android 8.0+ and ensure the phone supports Bluetooth 4.0 LE or newer; older stacks often produce audio dropouts or fail to report battery level.
Charge the phone above 20% and disable battery-saving modes that restrict background apps: Settings → Battery → Battery Saver off; also disable adaptive battery or aggressive app standby for the Bluetooth system app.
Enable location services if scanning fails (Settings → Location). On Android 12 and newer, grant Nearby devices/BLUETOOTH_SCAN and BLUETOOTH_CONNECT permissions to the app that manages Bluetooth if prompted.
Remove stale pairings: Settings → Bluetooth → Paired devices → tap the three-dot menu or gear icon and choose Forget/Unpair for any old entries that might interfere with a new session.
Clear the Bluetooth cache when encountering persistent discovery or pairing errors: Settings → Apps → Show system → Bluetooth → Storage → Clear cache (and Clear data only if you want to reset all Bluetooth settings).
Minimize RF interference: turn off or move away from other active headsets, Bluetooth speakers, and crowded 2.4 GHz Wi‑Fi equipment during the first attempt; a distance of 1–2 meters between devices reduces negotiation failures.
Update system components: install the latest OS patch (Settings → System → System update), update Google Play services and any vendor Bluetooth firmware via the manufacturer’s support app before initiating pairing.
If you want battery-level readouts on the phone, install a trusted companion app (for example, a battery-monitoring client) and grant notification and nearby‑device permissions so the app can report charge percentages.
Check Android OS version
Ensure your phone runs Android 7.0 (API 24) or later; for improved Bluetooth codec handling and stability aim for Android 11+, and upgrade to Android 13+ to gain native Low Energy Audio (LC3) support when the headset also supports it.
- Open Settings → About phone → Android version or Software information to read the OS release and security patch date.
- If About phone is absent, try Settings → System → About phone or use the search field in Settings for “Android version” or “Software information”.
- Check Build number and Android security patch level on the same screen; note both values when reporting pairing or audio problems to support.
- To see exact API level and release via USB: adb shell getprop ro.build.version.sdk (returns SDK_INT) and adb shell getprop ro.build.version. If you have any concerns regarding wherever and how to use 1xbet code, you can make contact with us at our web site. release (returns version string).
- Use Settings → System → System update to download official updates from the manufacturer; back up personal data before installing a major OS update.
Match OS capability with wireless features:
- Android 7.0+ – standard A2DP and HFP profiles for stereo audio and calls.
- Android 11+ – better vendor codec handling and overall Bluetooth reliability on most phones.
- Android 13+ – adds platform support for BLE Audio / LC3; both phone and accessory must implement it to benefit.
- Bluetooth hardware matters: Bluetooth 5.0 or newer is recommended for range, throughput and multipoint performance; verify chipset in Settings → About phone → Hardware information or the manufacturer spec sheet.
- Codec choices (SBC, AAC, aptX, LDAC) depend on phone firmware and accessory; codec selection appears in Developer options while a device is paired.
- Enable Developer options: Settings → About phone → tap Build number seven times.
- Open Settings → System → Developer options → scroll to Bluetooth audio codec and choose the preferred codec while the accessory is connected.
- For advanced debugging enable “Bluetooth HCI snoop log” in Developer options and collect the log for analysis if pairing or audio dropouts occur.
15 Best Little-Known Android Apps — Hidden Gems You Need to Try
This collection highlights 15 under-the-radar mobile utilities for Google’s smartphone platform across productivity, privacy, media and automation. Each entry in the main list includes: install size (MB), last update date, visible permissions, price model (free / freemium / one-time), and a concise one-line use case so readers can pick the right tool for a specific task.
Selection criteria: active maintenance (last update within 12 months), user rating ≥ 4.0 when available, realistic install footprint (preferably <50 MB), minimal access to sensitive permissions (avoid SMS/call access unless clearly justified), and clear data storage policies (local-only or documented cloud processing). Items flagged open-source include a direct repo link where possible.
Quick practical checks before installing: verify the permission list in the store listing, inspect battery usage in system settings after 24 hours, confirm whether backup/export exists, and test any automation rules in a sandbox profile. For network-blocking or VPN-based privacy tools prefer solutions that use a local VPN tunnel without routing traffic through third-party servers; expected CPU impact should remain low (<5% under light load).
The following entries are organized to show immediate value: one-line recommendation, concrete metrics (size, permissions, battery behavior), and the ideal scenario for deployment (offline task management, lightweight media processing, on-device encryption, or automation). Scroll down to find the item that matches a specific workflow and the exact installation footprint for planning storage and data usage.
Offline Notes: Lightweight Markdown Editor
Recommendation: Markor – offline-first, minimal Markdown editor with file-based storage, small footprint (<10 MB), open-source and usable without any network permissions.
- Core capabilities
- Local files: edit .md, .markdown, .txt and todo.txt directly in a chosen folder (internal storage or SD card).
- Live preview and split view: simultaneous editing and rendered output for faster formatting checks.
- Task lists: standard GitHub-style checkboxes (- [ ] / – [x]) with quick toggle support.
- Export & share: HTML export and share-to-print; open notes from any file manager or file mount.
- Small resource use: runs smoothly on low-RAM handsets, negligible battery impact when idle.
- Quick setup (3 minutes)
- Create a dedicated folder (suggestion: Documents/Notes).
- Open Settings → Files → Default directory → select Documents/Notes (permits SD access if needed).
- Settings → Editor → Autosave interval → set 3–10 seconds for fault-tolerant editing.
- Enable Split view in Settings → Viewer for on-device preview while typing.
- Practical templates and snippets
- Meeting note template:
– Date: 2026-03-16
– Attendees:
– Agenda:
– Action items: - Project header (YAML front matter):
—
title: Project X
tags: [project, backlog]
created: 2026-03-16
— - Quick task pattern:
– [ ] Task description @due(2026-03-20) #project
- Meeting note template:
- Search, organization and backups
- Use hashtags (#project, #meeting) and simple filenames (YYYY-MM-DD-meeting.md) for fast filtering with the built-in search.
- Periodic backup: copy the Notes folder to external storage or a mounted WebDAV/Nextcloud folder; an exported ZIP of the folder is handy for periodic snapshots.
- For sensitive content, place the notes folder inside a vault from a file-encryption tool (e.g., Cryptomator) or rely on system-level file encryption.
- Keyboard and workflow tips
- External keyboard shortcuts work: Ctrl+B (bold), Ctrl+I (italic), Ctrl+K (link) for faster composition.
- Create a small set of personal snippets (common headers, signatures) and paste them from the clipboard manager to save repeated typing.
- Use code fences for snippets:
bash
git status
- When to pick this tool
- Prefer Markor when offline-only access, tiny install size and file portability are priorities.
- Consider a sync-capable alternative if encrypted cloud sync and multi-device automatic syncing are required.
Quick start: create a note and sync later
Create a new note, set its sync mode to “Manual” (or mark as local-only), add a UTC timestamp to the filename like 20260316-1430-meeting. If you beloved this article and also you would like to get more info concerning 1xbet registration promo code kindly visit the webpage. md, then save to the local vault or folder. That guarantees a single-file record that can be synced later with no immediate network activity.
Use plain Markdown (.md) or .txt for maximum searchability and smallest file size; keep individual notes under 200 KB for fast uploads. For metadata, include a small YAML frontmatter:
—
created: 2026-03-16T14:30:00Z
modified: 2026-03-16T14:30:00Z
tags: [project-alpha, inbox]
sync: manual
—
Store inline images in a subfolder (attachments/) and reference them with relative paths: . Resize photos to ~1000 px on the long edge and compress to 300–800 KB before attaching to avoid long sync queues. If a rich capture is required, attach a PDF under 10–20 MB; larger binaries delay subsequent syncs.
When offline editing may collide, enable the app’s conflict policy that creates a conflict copy with timestamp and device name, e.g. meeting-notes-conflict-20260316-1530.md. Resolve by opening both files and using a three-way text merge or copy-paste; preserve the earlier file’s created timestamp in the frontmatter where possible.
Recommended sync settings for deferred uploading: set network to “Wi‑Fi only”, enable “Sync on demand” or “Manual sync” and schedule background attempts at 15–30 minute intervals when charging. If background sync is desired, whitelist the note application in the system battery optimizer to prevent kills during long uploads.
Choose a remote host that matches the privacy model: Nextcloud or WebDAV for self-hosting and folder-level control; Dropbox for reliable delta sync; Google Drive for wide availability. For end-to-end encryption, enable the app’s built-in encryption or use a zero‑knowledge provider; keep the encryption passphrase backed up in a separate password manager–losing it means irretrievable notes.
Batch sync process: group related files into one folder, run a manual “Sync now” when on trusted Wi‑Fi, confirm sync log shows successful PUT/UPLOAD for each file, then check timestamps and frontmatter “modified” values. If transfers fail, retry with exponential backoff (15s, 30s, 60s) or switch to manual export of changed files via the share/export feature.
For quick captures from other applications, use the system share sheet to append content to an existing file or create a new note named with a fast prefix like INBOX-20260316.md. Keep inbox files short; triage them into project folders during the next sync session to maintain a clean folder structure: /notes/2026/03/, /projects/project-alpha/.
- Core capabilities
Oppo A77s Android Version — What Android Does It Run? (Specs & Updates)
Recommendation: Install the vendor-supplied build that maps to Google’s mobile operating system 13 or later to get current security patches, improved app compatibility (64-bit support and modern APIs), better battery management and the latest privacy controls. If the device still runs an older platform release, schedule the official OTA download over Wi‑Fi and back up personal data first.
How to verify the installed build: Open Settings → About phone → Software information (look for Platform release, Build number and ColorOS entry). A matching example string is: Platform release: 13 · ColorOS 13.0.x · Build: CPHxxxx. Note the security patch date shown on the same screen – anything older than three months is a reason to fetch the latest available update.
How to update safely: Settings → Software Update → Check for updates → Download and install over Wi‑Fi. Ensure battery ≥50% or keep the handset charging, and create a backup (cloud or local) before applying a major platform upgrade. For manual installs, use the official support page from the manufacturer and the phone’s built-in local upgrade option; avoid unofficial ROMs unless you are experienced, as they can void warranty and break network features.
Post-update checklist: Confirm the new Platform release and security patch date in Settings → About phone; open frequently used apps to confirm compatibility; run a quick benchmark or battery-monitoring session if you track performance. Enable automatic updates and scheduled installation to stay current without manual checks.
Quick Android Overview
Check Settings > About phone > Software information to confirm the platform build number and Security patch level; note the build ID for support tickets and firmware searches.
Open Settings > Software update (or System update) and enable automatic installs over Wi‑Fi; apply full platform upgrades while the handset is charging and connected to a stable network to avoid failed installs.
Target a security patch cadence of monthly, or at worst quarterly; if patches stop arriving for more than 90 days, contact the device maker or your carrier to confirm the update policy and timeline.
Use Play Store > Profile > Play Protect and enable “Improve harmful app detection”; run a manual scan after sideloading APKs or installing lesser‑known apps.
Audit runtime permissions at Settings > Privacy > Permission manager and revoke camera, microphone, location or SMS access for apps that don’t need them; set permissions to “While using the app” where possible.
Control background activity via Settings > Battery > Battery usage: restrict background work for high‑drain apps, enable Battery Saver profiles during extended use, and whitelist essential apps only.
Keep regular backups: Settings > System > Backup – enable cloud backup (Google Drive or manufacturer cloud), verify restore on a second device or via an emulator, and export contacts and photos separately.
If you plan custom firmware or rollbacks, read the warranty implications, download official factory images from the support portal, and back up EFS/IMEI data first; avoid unlocking the bootloader unless you accept potential service limitations.
Protect access: enable a secure lock method (PIN/password), set up biometric unlock with fallback, and activate Find My Device/remote erase to recover or wipe the handset if lost or stolen.
Android version at launch
Recommendation: open Settings → About phone right away to confirm the preinstalled build and security patch level, then install any available firmware patches before adding banking or work accounts.
- Factory software shipped: ColorOS 12. Should you loved this information and you would like to receive much more information about 1xbet app login assure visit our own website. 1, built on Google’s mobile OS 12 (check the build name under About phone to confirm the exact release).
- Maintenance expectations: units in this segment typically receive one major system upgrade plus around two years of security patches; verify the official support policy for precise timelines.
- How to check for upgrades: Settings → System (or Software) → System upgrades → Check now. If an upgrade appears, download over stable Wi‑Fi and install when battery is above 50%.
- Pre-upgrade checklist:
- Full backup of user data (cloud or local).
- Free storage of at least 3–5 GB for the installer.
- Battery charge minimum 50% or keep the phone plugged in during the process.
- Post-upgrade actions: confirm the security patch date under About phone, re-authenticate critical apps, and test connectivity and camera functions.
- If no official upgrade appears: confirm carrier-supplied firmware, consult the manufacturer support page, or visit an authorized service center; avoid unofficial builds if you require warranty coverage.
- App compatibility: keep Google Play Services and Play Store components current to ensure apps leverage new platform features and security fixes.
What Android Version Is Oreo? – Android 8.0 & 8. Guide
Recommendation: Upgrade devices to the 8.1 build of Google’s mobile platform when available – it contains the latest fixes, final API updates for the 8.x line, and the stronger security baseline compared with the initial 8-series release.
Public rollout began August 21, 2017 (API level 26); the maintenance update arrived December 5, 2017 (API level 27). Key capabilities introduced with the 8.x releases include notification channels, picture-in-picture, autofill framework, adaptive icons, background execution limits, Project Treble for faster vendor updates, Wi‑Fi Aware (NAN), Vulkan 1.0 support and improved battery management.
For app developers: set compileSdk and targetSdk to API 27 where possible, migrate notifications to channels, replace long-running background services with JobScheduler/WorkManager, implement the autofill API for credentials, add support for adaptive icons, and run compatibility tests on devices and emulators at API 26 and 27 to catch behavior changes such as stricter background limits and new permission behaviors.
For device owners and IT admins: prefer manufacturer builds that include monthly security updates; choose devices with Project Treble support to improve upgrade prospects; if vendor updates stop, evaluate community-supported builds or plan hardware refresh to maintain security and access to modern APIs.
Quick Identification of Oreo on Your Device
Open Settings → About phone → Software information and confirm the OS entry shows API level 26 or 27, or a build string that begins with the letter “O”.
If the About screen lacks API info: tap Build number seven times to enable Developer options, then reopen About or Developer options and read the Build number; Oreo-era releases commonly use build prefixes like OPR or OPM (the leading “O” indicates the 8.x family).
Fast visual checks: look for notification dots on app icons, built-in picture-in-picture behavior when a video app is sent to the home screen, and adaptive icon shapes on the launcher. Try selecting text inside a message: smart text selection should show contextual actions (call, map, copy) in a small floating toolbar.
Notification changes: long-press an active notification to reveal channel controls or tap the gear/Details button to open notification categories. Swipe a notification slightly and tap the clock icon to snooze it–these controls are characteristic of the 8.x release.
Autofill and app access: open Settings → System → Languages & input (or Search in Settings for “Autofill”) – presence of an Autofill service entry and a dedicated Picture-in-picture list under Apps & notifications → Special app access are strong indicators of the 8.x build.
Prefer a tool: install a system-info utility such as AIDA64 or CPU-Z and check the “OS / SDK level” field; a reported SDK of 26 or 27 confirms the 8.x family without relying on vendor labels.
Open Settings → About phone to check version
Open Settings → About phone and inspect the entries labeled “Software information”, “Build number”, “Security patch level” and “SDK” to get the exact release identifier and build string.
- Open Settings and tap About phone or About device. If you see a search icon, type “About”.
- Tap Software information (on some models it appears as Software info or About phone → Software). Look for fields named Release, Build number, or Baseband.
- If the release string is not visible, tap Build number seven times to enable Developer options; then check Settings → System → About phone again or use Developer options to reveal additional details.
- For an exact numeric identifier, find the SDK entry or the numeric part of the release string (example format: X.Y.Z or X.Y). The SDK is an integer that maps to a specific platform release.
- If the Settings UI omits these labels, open Settings → System → Advanced → System update; some vendors place full software info there.
- Use the device boot screen: many phones show the build string or release during startup or on the recovery screen.
- If you have a PC available, run: adb shell getprop ro.build.version.release (returns the release string)
- Also useful: adb shell getprop ro. If you treasured this article and you also would like to get more info regarding 1xbet apk download generously visit our own website. build.version.sdk (returns SDK integer) and adb shell getprop ro.build.version.codename (returns codename if present).
- Compare the SDK integer and release string against a trusted mapping table to identify the specific platform release used on the handset.
If Settings reports only a codename or a non-numeric label, collect Build number and Security patch level and search those strings on the vendor support site to confirm the exact release applied to that device.
Poco X3 Pro Android Version – Which Android OS Does It Run?
Recommendation: Keep the phone on the latest MIUI release you can install from official channels (MIUI 12.5 Enhanced or MIUI 13 builds) because those packages preserve stability and vendor drivers while delivering security patches; if you require a newer underlying Google mobile operating system major release, prepare to move to a community-maintained ROM after validating hardware support.
Factory state: the model shipped with MIUI 12 on an AOSP-based Google mobile OS 11 core. Official updates delivered MIUI 12.5 (Enhanced) and later MIUI 13 packages, but those updates retained the same underlying OS 11 base rather than advancing the major Google platform level. Check Settings → About phone → MIUI version and Security patch level to confirm which build and patch date your unit currently runs.
If you want more recent platform features or an upgraded major Google mobile OS base (12 or 13), practical options are: 1) choose a maintained aftermarket build such as LineageOS or Pixel Experience that explicitly lists support for this device and the target platform; 2) unlock the bootloader, make a full TWRP (or equivalent) backup, and test ROMs on a secondary device or after a full NANDroid backup; 3) verify modem, camera and Widevine status post-flash – Camera HAL and DRM often break on unofficial builds.
Security and daily use guidance: install official MIUI OTAs when available, apply monthly or quarterly security packages listed in Settings, and avoid random unsigned firmware packages. If you opt for a custom release, prefer actively maintained forks with recent security commits and a clear changelog; otherwise keep the official MIUI 13 build for the best balance of performance, camera reliability and carrier compatibility.
Current Android Version on the Poco X3 Pro
Recommendation: Open Settings → About phone → Software information and install the latest stable MIUI OTA available; the handset originally shipped with MIUI 12 on OS 11 (API 30) and received the official MIUI 13 upgrade based on OS 12 (API 31).
To verify the exact build and patch level: go to Settings → About phone → Software information and note the MIUI version string, OS release (numeric level) and Security patch level date. Use the built‑in Updater app for official over‑the‑air packages; save a full backup before applying manual packages or fastboot images.
If you require a newer major OS level than provided by the manufacturer, check community ROMs (LineageOS, crDroid and active XDA threads) for maintained builds targeting OS 13 or later; confirm device codename support, active maintainer, known issues and required recovery/bootloader steps. Unlocking the bootloader and flashing custom firmware voids warranty and carries risk of data loss.
For security cadence: prefer official OTAs for monthly/quarterly security fixes; compare the Security patch level in Software information with the device support page to determine whether an update is pending or already applied.
Identify Android OS and MIUI base in Settings
Open Settings → About phone and read the “OS version” and “MIUI version” lines; if unclear, verify with the commands shown below.
-
Quick check in Settings:
- Settings → About phone → OS version – displays the underlying OS release (example: 11).
- Settings → About phone → MIUI version – shows MIUI release string (example: MIUI 12.5.6.0 RKHMIXM) and often the ROM branch (Global / China / EEA / IN).
- Settings → About phone → Security patch level – shows latest security update date (example: 2024-02-05).
- Settings → System update → Update details – release notes frequently state the exact OS base used for that MIUI build.
-
Interpret MIUI string:
- MIUI number at the start = MIUI release (e.g., 12.5, 13).
- Parentheses or trailing code usually contain device codename + region tag (look for EU, IN, GLOBAL, CN, etc.) to determine ROM channel.
- Build ID and incremental fields identify incremental firmware and can be matched to Xiaomi/third-party changelogs.
-
Verify with a USB connection (fast, exact):
- Run adb shell getprop ro.build.version.release – returns the OS release number (example output: 11).
- Run adb shell getprop ro.miui.ui. If you have any queries regarding in which and how to use 1xbet promo code for registration, you can get in touch with us at our own internet site. version.name – returns MIUI name (example output: V12.5).
- Run adb shell getprop ro.build.version.incremental – returns build identifier.
- Run adb shell getprop ro.build.version.security_patch – returns security patch date.
-
If Settings and adb disagree:
- Check for a custom ROM or unlocked bootloader (Settings → Additional settings → Developer options → Build number) and compare build fingerprint via adb shell getprop ro.build.fingerprint.
- Cross-check MIUI update server pages or the official updater app changelog using the exact MIUI build string to confirm the OS base claimed by the firmware.
-
Practical checklist to copy or screenshot:
- Take a screenshot of About phone showing OS version, MIUI version and Security patch.
- Record adb outputs for ro.build.version.release, ro.miui.ui.version.name and ro.build.version.security_patch.
- Match MIUI build string against official release notes to determine exact OS base and ROM channel.
-
